Zero-Trust inherently distrusts any device or network until they are proven to be safe.
One method of enforcing Zero-Trust principles on mobiles is by blocking access to business resources from devices that are high risk or have not been verified as trustworthy.
Trustd acts as a Policy Enforcement Point, providing access to your Microsoft Cloud Apps only to trusted mobile devices.
The Trustd app assesses the security risks of every mobile device in your workforce, returning a security health status to the Trustd dashbaord, which in turn talks to Microsoft Entra ID to grant or deny access to your Microsoft Cloud apps.
Using the integration with Microsoft Entra ID, Trustd is able to prevent access to business information for mobile devices in the scenarios where access would be determined as high risk (high risk being where a device is compromised or trust has not been verified).
Examples of these scenarios are provided below and represented in the diagram in figure 1.1:
- The user Alice is protecting one device with Trustd but has not installed Trustd on her corporate device (after the admin has specified that she should). The admin is notified and she is prevented from accessing business data on either of her mobiles until such a time that she protects both devices, where access will be automatically restored.
- The user Sarah is stopped from accessing business data on her personal mobile as she hasn’t protected the device with Trustd.
- The user John is stopped from accessing business data on either of his mobile devices as his corporate device is high risk. Access to business data will automatically be restored once he resolves the high risk events on the device.
- The user Bob is able to access business data from both his personal and corporate device, as both are secured with Trustd and in a low risk state.
Figure 1.1 Logical diagram of integration, with user stories
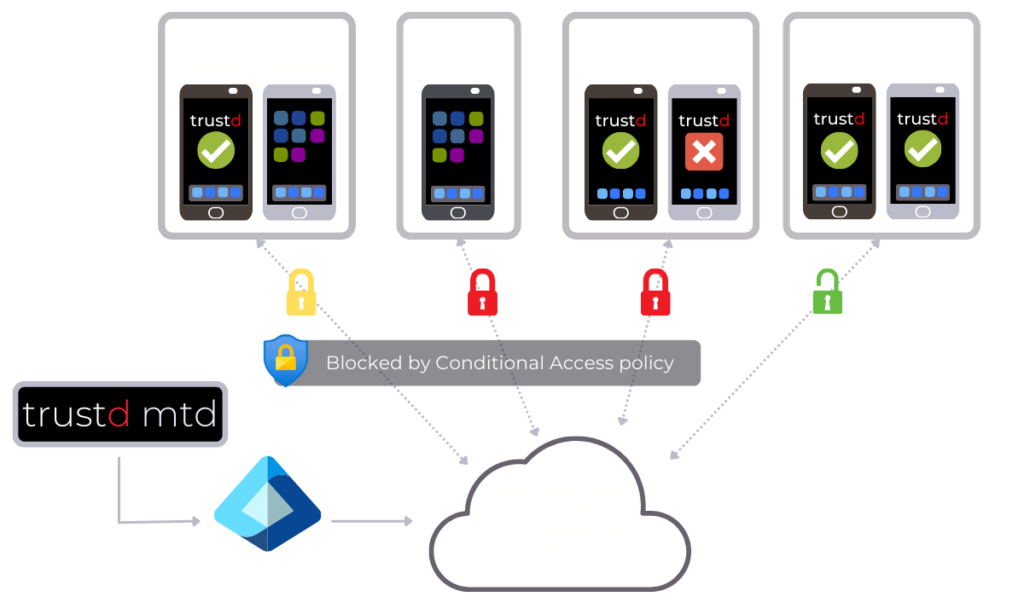
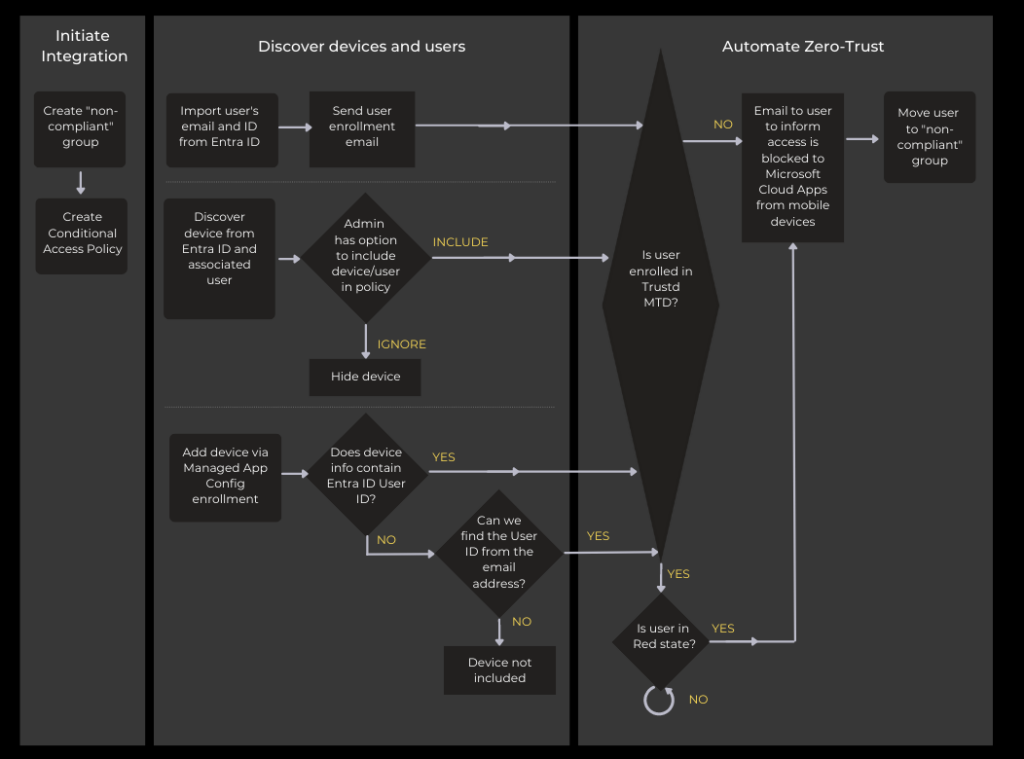
Fig. 1.2 Technical flow
Trustd’s unique approach to Zero-Trust means that it is the only single-solution Mobile Threat Defence (MTD) that enables your Zero-Trust strategy for all of your mobile devices, whether they’re managed by an MDM/MAM or not.
Free Zero Trust white paper
We explain how Zero-Trust for mobiles works in practice, as well as how Trustd is unique in its approach. Download now.

