When it comes to compliance on mobile devices, Trustd does the hard work.

Why become Cyber Essentials certified?
If you’re committed to improving your organisation’s cybersecurity posture, the UK’s Cyber Essentials certification demonstrates your data safety chops to customers, prospects and partners.
Effective cyber security is a journey rather than a destination.
Jon Coss, JC Cybersecurity
With more data, more points of access, and a distributed workforce, the ability to prove that you take cybersecurity seriously has become a non-negotiable factor in many requests for tender. In fact, some organisations mandate that their suppliers have Cyber Essentials certification.
Trustd makes compliance easy
We designed Trustd to make it easy for small and medium businesses to protect their mobile devices from attack. We’re Cyber Essentials-certified ourselves, so we know that by using Trustd you can tick off all these requirements.
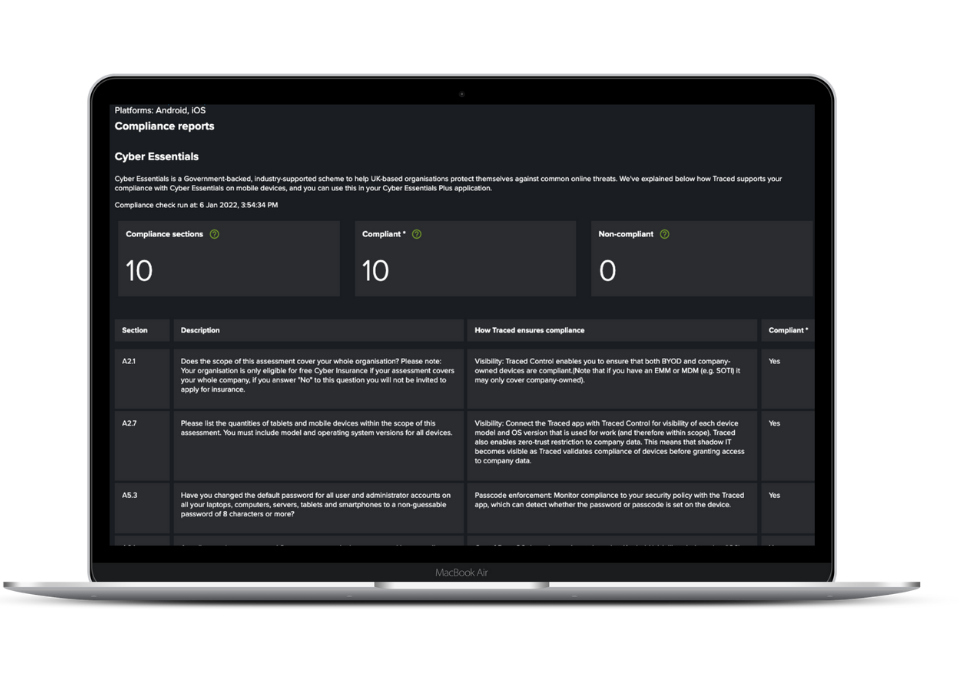
So we created the Compliance report within the Trustd console and cross-referenced all the mobile device aspects of the UK’s Cyber Essentials requirements with how you can meet them using Trustd.
- Copy and paste responses: We explain how Trustd ensures compliance for each mobile-related section of the Cyber Essentials framework. So if you’re compliant, you can just copy and paste the details into your application.
- Compliance summary: See at a glance, in real time, how your organisation’s mobile devices stack up against the requirements, so you can take steps to ensure full compliance across the board.
What’s covered?
Trustd Mobile Threat Defence provides a comprehensive, all-in-one solution to cover Cyber Essentials compliance on employee devices. Whether you’re operating a COxx or BYOD strategy, you can roll Trustd out to all devices without invading employee privacy.
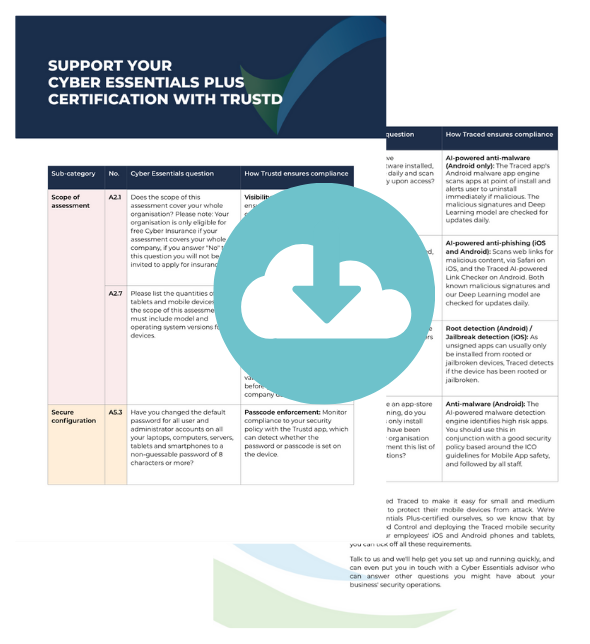
In particular, Trustd can ensure mobile device security via:
- Company-wide security
- Visibility of device model and OS
- Passcode enforcement
- Out-of-date OS/jailbreaking
- Anti-Malware and Anti-Phishing
Download our infosheet to see exactly how Trustd supports Cyber Essentials.
How Trustd helps
Support your Cyber Essentials certification easily with Trustd MTD
Any business that uses mobile devices has a duty to its customers, employees, and partners to make sure they are doing everything in their power to protect against cyberthreats.
A simple and effective way to do so is with Trustd. Quick and easy set up, you can enrol your organisation’s devices within five minutes to protect BYOD, COBO or COPE devices from phishing and other malware, credential theft via compromised WiFi, device vulnerabilities, and malicious web and app content.
Try it for yourself
Get immediate access to the Cyber Essentials report in the Trustd console to see where you’re compliant and where you aren’t. We can get you set up straight away, and can even put you in touch with a Cyber Essentials advisor who can answer other questions you might have.
