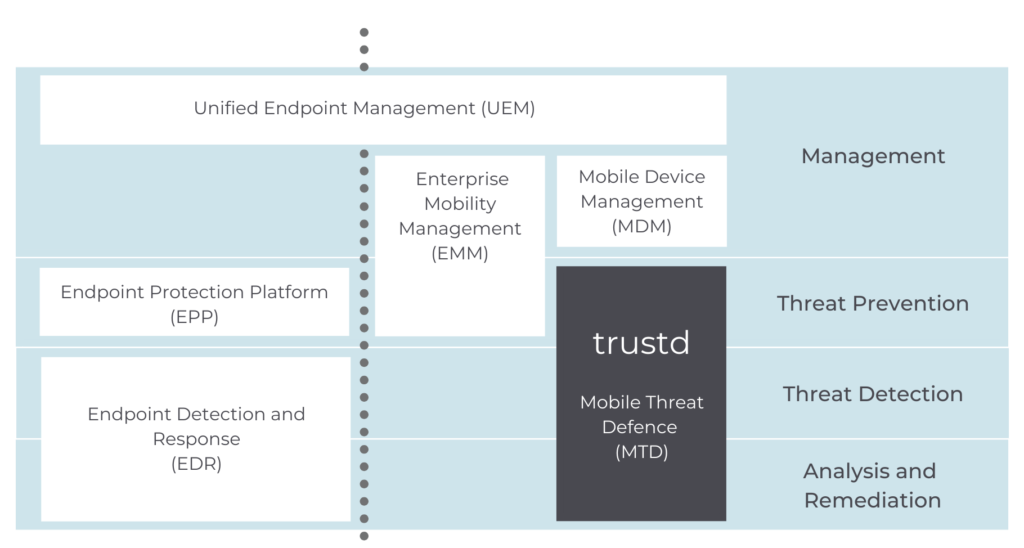
You may already have a Mobile Device Management (MDM) solution in place and are wondering how Mobile Threat Defence (MTD) fits in. Or perhaps you’re part of the 61% of organisations that have no mobile security in place and are researching your options?
How are they different?
Quite simply, MDM is just for managing your organisation’s devices – it can deploy policies wholesale, restrict access to particular apps or services, or act as a VPN. However, it doesn’t have any threat detection, analysis or remediation capabilities. So it can’t block phishing, stop malware, guide users to remove threats, identify permissions abuse on Android, or scan WiFi networks for attacks.
MDM has been around much longer than MTD, and many organisations have recognised the need for basic mobile security and adopted some form of MDM. However, they’ve run into some significant challenges, and that’s led to MTD solutions being developed – to specifically address those challenges and shore up the threat protection aspect of mobile security.
If you’ve already got MDM, do you also need MTD?
If you’ve got Mobile Device Management (MDM) already, you’re already a step ahead of most businesses.
However, as we explained above, MDM only deals with the management side of mobile devices, and can help to put a secure fence around sensitive data. It doesn’t offer any means to stop those threats from entering the perimeter in the first place. Only Mobile Threat Defence (MTD) can currently do that.
Some MDM providers offer some MTD features in their solution, and if you have a unified endpoint solution that covers your desktop security, sometimes the vendor will offer mobile security as an optional paid extra to your license.
The problems with these two options are 1) performance and 2) cost.
MTD providers (like us!) are specialists in mobile threats, and our protection is designed around identifying and stopping those threats – not repackaging desktop threat protection as a mobile solution, which is what many cybersecurity vendors do. Why would you settle for security that only catches some of the attacks?
Here’s an analogy: If MDM is like hiding your valuables from burglars, MTD is like locking the doors and windows beforehand.
No MDM? No problem.
Trustd protects devices and restricts access to company data for untrusted devices whether they are managed by an MDM/MAM or not.
Whether your organisation already has some level of mobile security or management or not, we priced our MTD, Trustd, to ensure that cost wasn’t a barrier. But if you don’t have an existing MDM or MAM in place, that doesn’t matter either, as Trustd can also be deployed as a standalone MTD across your whole organisation, in just a few minutes.

