Many businesses are looking to containerisation to solve their BYOD or COPE security concerns, but it’s not as effective at stopping mobile threats as you might think.
Let’s explore why this is, and how layering Mobile Threat Defence on top of your Intune, MDM or Android Enterprise containerisation model adds significantly more protection.
Firstly, what is containerisation?
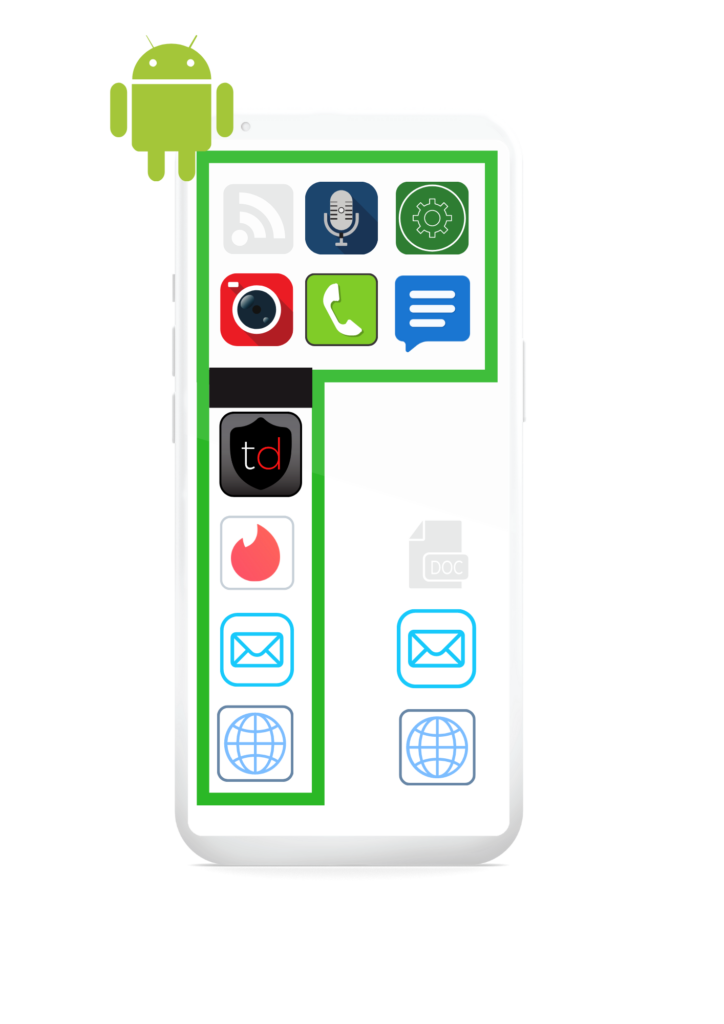
Quite simply, containerisation is about splitting up apps and data on a phone into two “containers” – one for work stuff and one for personal stuff.
The personal container, or ‘profile’ might include emails, personal contacts, games and apps, photo gallery, personal call logs etc. The work profile might also have these things, but duplicated in a separate container that is dedicated to business use.
That way, if there’s a threat or data breach, the business can quickly and easily shut off access from individuals’ devices to the work container to halt the spread of infection through the company network or until the threat to business data is remediated.
The main drawbacks to containerisation are around the additional work required for IT teams: a) it’s complicated and confusing for the end-users to set up, which can lead to more support tickets and potential pushback from employees around privacy, and b) it also needs ongoing IT resource to setup, manage and maintain.
On the other hand, it’s a useful system for securing BYOD or COPE devices because the personal profile is unmanaged and invisible to the employee’s company, but on the work profile the business gets control over what apps are installed and what access a user has to business systems.
Why containers aren’t enough to prevent data breaches
The problem arises because some elements of a device’s functionality are shared between the work and personal profiles. For example, SMS, OS settings and network preferences can’t be separated into the two different profiles.
Also, the company has no control or visibility over the shared resources or personal profile, if the whole device is compromised. And as the container and even the MDM or UEM that manages the containers doesn’t come with any inherent threat detection or remediation, the company may not even realise the device has been compromised – and so not stop it connecting to the business network or data.
What mobile threats can bypass containers?
- Phishing – Links in SMS, messaging apps, social media and emails can point to fake websites designed to steal credentials or get the user to install malware on the device.
- SMS 2FA/OTP interception – Some malware hijacks 2FA/MFA SMS passcodes to send them to the attacker or deletes them entirely.
- OS vulnerabilities – Out-of-date OS versions, rooting or jailbroken devices or accessibility configurations can compromise a device
- Malware – Overlays, keyloggers, ransomware and spyware can all be installed on the device by a successful phishing attack, a malicious app, or installed directly.
- Man-in-the-Middle attacks – Compromised WiFi networks can intercept all data, including credentials, to and from the device.
Therefore, it’s crucial that you add some form of threat detection and remediation on top of your containerisation on the device. Trustd protects employees’ Android and iOS mobile devices against all the threats above with AI-powered anti-malware (Android only) and anti-phishing, WiFi network scanning and OS vulnerability detection.
How can you use Trustd MTD with containers?
Trustd Mobile Threat Defence can be deployed in containered environments – adding significant value and protection on top of your device management.
For work containers:
Typically, containerisation is provided via an MDM (e.g. Intune’s App Protection Policies). This makes deploying Trustd to work containers across your devices as easy as pressing a button. Trustd’s Zero-Trust support means you can also easily block access from unsecured or compromised mobile devices to your Microsoft Cloud Apps.
In personal containers:
Trustd can also be deployed in the personal container as users can enrol via email with a few taps. And our privacy-first ethos ensures all employee activity remains private – all you see is a Red-Amber-Green risk status of the device.